Key Takeaways
1. Black box testing assesses system functionality without knowledge of its internal workings, simulating external attacks to uncover hidden vulnerabilities.
2. White box testing examines a system’s internal code, data flows, and architecture to identify vulnerabilities that are not visible in black box testing.
3. IS Partners performs penetration tests to help businesses equip their systems with the most appropriate security controls.
What Is Black Box Testing?
Black box testing is a blind software evaluation technique. It mimics an external attack without prior knowledge about the system’s structure.
It helps companies:
- Test for vulnerabilities in their network infrastructure—such as unpatched services, misconfigurations, or open ports—and mobile applications.
- Evaluate the security of devices connected to the company’s network, e.g., mobile devices, servers, computers, and tablets.
This “blind testing” forces the auditor—an ethical hacker or penetration tester—to spontaneously find an open route access into the network. The idea is to catch vulnerabilities that might be overlooked.
Ideally, the tester will not find any vulnerabilities. If they do, corrections can be done before an actual hacker finds that same route.
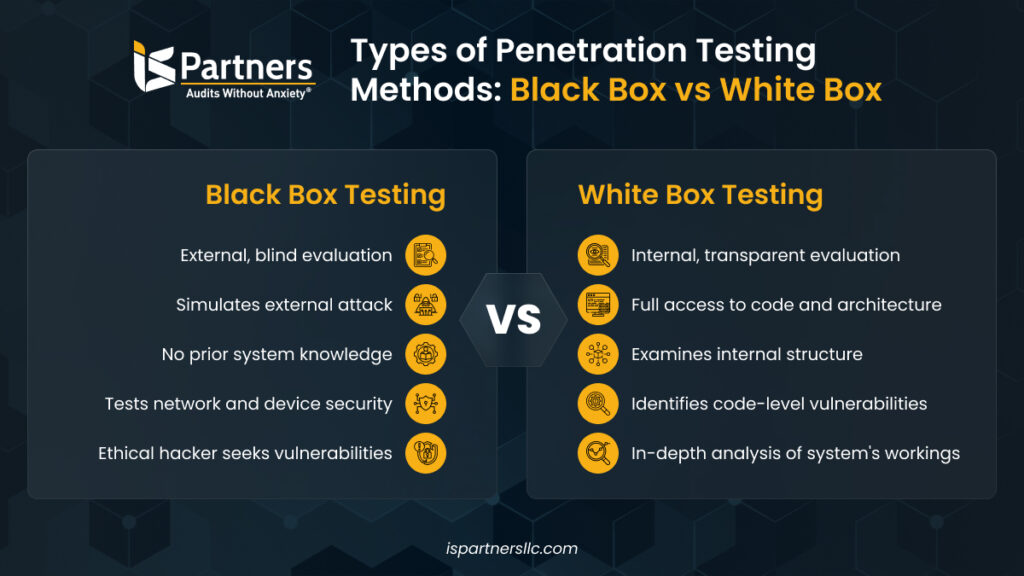
What Is White Box Testing?
White box penetration testing is also known as clear box testing, glass box testing, transparent box testing, and structural testing.
With this type of advanced pen testing, your tester will have complete access to your source code, network protocols, and control structures. This test will help the tester know where to look for security issues.
The test still requires the evaluator to perform an in-depth analysis of your software or system’s internal structure. They typically look for security vulnerabilities such as butter overflows, SQL injection vulnerabilities, authentication flaws, data leaks, and permission issues.
Black Box vs. White Box Testing: How Are They Different?
Here’s a table that summarizes the key differences between black box, white box, and gray box testing.
| Parameter | Black Box Testing | White Box Testing |
|---|---|---|
| Testing Objective | Ensure a system works flawlessly for the end user | Ensure an application code is high-quality |
| Focus | Focuses on validating the output against the expected result for given inputs | Focuses on internal code structure, paths, and logic |
| Performed By | Testers who do not need coding knowledge | Developers or testers with programming skills |
| Scope | Generally less extensive and focused on specific functionalities, so quicker | Covers all code paths, conditions, and loops, so more time-consuming |
| Types | Functional testing, system testing, and acceptance testing. Testing is based on system requirements and use cases (user feedback) | Unit testing, integration testing, and code coverage analysis. Testing is based on code logic, flowcharts, and design documents |
| Programming Knowledge | Not required | Required |
1. Testing Objective
Black Box Testing
Black box testing is used when you want to perform an external assessment to test your security posture.
Since most hackers are not aware of your system’s internal workings, they are considered “blind.”
You can also use it to test:
- Large or complex systems. When the system is large or complex, examining the code might not be feasible. In such cases, black box pen testing is a good choice to look for system vulnerabilities.
- System performance under real-world conditions. Black box pen testing is the closest you can get to an actual breach attempt by a potential hacker. It shows you exactly how your system will respond to an actual attack and whether it is capable of warding it off.
White Box Testing
White box security testing is used when you’re testing a critical system because it helps you perform thorough checks on its defenses.
Since the tester has complete access to your system, they can evaluate your code paths, identify vulnerabilities, and perform checks on data encryption and protection to find vulnerabilities that a black box test may not have found.
Organizations use white box testing when:
- A system’s performance needs to be tested. White box pen tests find bottlenecks and poorly optimized algorithms.
- A system handles sensitive customer information. If your software application handles sensitive information, you can use white box testing to evaluate your database security and make sure all security controls are working well.
2. Focus
Black Box Testing
Black box testing focuses on analyzing your system’s external behavior through inputs (the tester’s actions) and outputs (how the system responds).
The tester assesses how your system responds to each attack vector, such as input tampering, authentication breaches, and unauthorized access.
This type of testing is an end-to-end approach that’s limited to your system’s external interfaces that impact the end-user, such as web servers, databases, integrated systems, and user experience and user interface.
White Box Testing
White box testing focuses on a detailed examination of your system’s internal paths and code. It examines how data flows through your entire system, how different components interact with that data and each other, and how secure your control structures are.
These tests also look at your system code to find inefficiencies, weak encryption uses, and logical errors that could create potential security issues. In these cases, the tester will use their programming knowledge to find security issues.
3. Qualified Evaluators
Black Box Testing
Black box testing is performed by external security testers, certified ethical hackers, or penetration testers.
White Box Testing
Developers, security analysts, or people with expert knowledge of your system architecture (data flows, control structures, etc.) and codebase typically perform white box tests. Developers typically perform white box testing.
4. Types
Black Box Testing
Methods for black box testing are classified based on the purpose of testing. Here are the two most common types of black box testing:
- Functional testing. This type of testing verifies that the system inputs and outputs work as intended. It includes smoke, sanity, integration, regression, system, and user acceptance testing.
- Nonfunctional testing (NFT). NFT evaluates a system’s ability to handle threats, resist attacks, and maintain performance under stress without knowing about the internal code structure. It includes usability, load, performance, compatibility, stress, and scalability testing.
White Box Testing
White box testing methods are classified based on the software aspect that is in focus. Here are a few types of white box testing:
- Unit testing. Unit tests help you ensure that each component of your system functions as it should.
- Integration testing. It is performed after unit testing and focuses on whether each component tested works with others, i.e., it tests the interfaces between each component.
- Regression testing—This ensures that recent changes work as intended and do not negatively affect the usage of the system. It involves re-running tests to confirm that the system still behaves correctly.
5. Applicability
Black Box Testing
Black box testing is typically performed at the end of comprehensive testing processes because it checks how the system behaves from the outside and helps find bugs that might affect the system’s security.
However, it can be performed by itself to check for security vulnerabilities in a system, especially if it works with sensitive data.
White Box Testing
White box testing is used at the early stages of the development and integration phases to find vulnerabilities, logic errors, and security flaws within the code and improve software quality.
6. Timeframe
Black Box Testing
Black box testing focuses on system functionality, not its inner workings. It can be performed once the code has any functionality. Automated testing is typically quick, but the time frame depends on system complexity.
White Box Testing
White box testing can take days, weeks, or even months. Testers must run every scenario on all paths and code lines to ensure security and bug-free code. This can extend the software development lifecycle.
7. Techniques and Tools Used
Black Box Testing
All black box testing techniques focus on an external vulnerability that might be exploited. Some of the common testing techniques are the following:
- Port scanning. Scans system ports to identify open ones and the vulnerabilities of the services running on them.
- Exploratory testing. Tests known vulnerabilities to see how the system reacts.
- Fuzz tests. Sends random or invalid input to check if the system crashes or behaves unexpectedly.
- Password cracking. Tests the system’s resistance to brute force attacks and password vulnerabilities.
- Equivalence testing. Groups inputs and tests one value from each group to cover possible outcomes.
- Vulnerability scanning. Uses tools to scan the system’s IP for known vulnerabilities.
- Web scraping. Gathers data from web pages to test how far a web application can be accessed.
White Box Testing
White box testing techniques include:
- Statement coverage. Tests the functionality of each code block and checks if all statements are logically built.
- Data flow testing. Analyzes data paths through the system to see how data structures impact program flow.
- Path testing. Tests all possible routes in the program to ensure every scenario and line of code is covered.
- Control flow testing. Tests the execution order of statements and branches in the source code.
8. Process
Black Box Testing
Usually, black box penetration testing follows the following five steps:
- Reconnaissance. Gather information about the system, including IP addresses, DNS records, and employee details.
- Scanning. Collect deeper system details like software, operating systems, and user information.
- Discovering vulnerabilities. Use tools to find system vulnerabilities based on the gathered data.
- Exploitation. Exploit identified vulnerabilities to access the system and cause maximum damage quickly.
- Reporting and cleanup. Report findings and restore the system to its original state.
White Box Testing
White box penetration testing typically follows the below steps.
- Select areas to test. Narrow down core system areas for testing and gather information on the programming language and development tools.
- Identify code to test. Outline the specific lines of code to be tested, detailing their functions and expected outputs.
- Write test cases. Create test cases based on the vulnerabilities being assessed.
- Execute testing. Test each scenario to uncover system vulnerabilities.
- Analyze results. Review test results to plan fixes for vulnerabilities and record all findings and strategies.
How To Choose the Right Penetration Testing Technique
Choosing the right penetration testing technique is crucial for effectively identifying vulnerabilities that could be exploited. A well-selected approach ensures comprehensive coverage and tailored assessments, ultimately enhancing an organization’s security posture.

1. Identify Your Goals
Clearly define what you want to achieve with a penetration test. Do you want to identify vulnerabilities, test your incident response capabilities, or get an overall assessment of your security posture?
At this point, you also need to know the scope of the test. This means deciding which systems, networks, and applications will be included.
IS Partners’ Information Security consultant shared his thoughts about the importance of clearly identifying the objectives of the penetration testing,
The goals can differ depending on how mature an organization’s security posture is. For a company with a newly created security policy, a Blackbox test can make more sense as a first test to ensure their public-facing infrastructure is secure. Then, as a follow-up, a Whitebox test can be performed. For an organization with a mature and long-standing security policy, a Whitebox test as the first step can make more sense.
2. Determine What You’re Testing
Find out exactly what you’re testing. Are you going to focus on a web application, network infrastructure, cloud environment, or mobile app? What are the programming languages, operating systems, and security mechanisms they use?
You need to know the exact technologies of the system you’re testing if your goal is to perform a thorough test.
3. Review Compliance, Regulatory, and Audit Requirements
Review your industry’s compliance, regulatory, and audit requirements to ensure that you meet all necessary standards and whether the pen testing method you’re looking to use is compatible with them.
For instance, if you’re working in the finance sector, you’ll need to comply with the Payment Card Industry Data Security Standard (PCI DSS). This will require you to conduct regular penetration tests to identify vulnerabilities.
4. Consider Your Resources
Determine whether your team has the necessary skills, time, and budget to perform all the types of testing that fit your goals and scope. Your team knows your systems, applications, and potential vulnerabilities well, so they’re best suited to performing internal testing.
But if your internal team lacks the expertise or if the testing scope is too extensive, outsourcing to a specialized provider like an IS Partners might be the best option. This way, you don’t have to pull resources away from other critical tasks.
5. Analyze the Potential Impact
Determine the impact of your decision, especially if you’re considering white box testing. That’s because this type of testing could potentially disrupt services or expose sensitive data if not handled carefully.
Before going forward, conduct a thorough risk assessment to understand the possible consequences of testing, such as downtime, data corruption, or even compliance breaches.
6. Get Expert Opinion
Before making a final decision, consider talking to an expert.
A penetration testing provider like IS Partners can help you understand the strengths and limitations of different testing approaches. Our seasoned experts can help you determine the best-fit approach for your operations.
How To Choose the Right Pen Testing Provider?
Choosing the right pen testing provider is important so that their services are in line with your requirements and expectations. Here are a few useful tips to help you make the right choice:
- Identify your requirements and assess your specific needs. Do you need to engage a pen testing provider for a one-time task, or is it an ongoing requirement? What areas and systems do you need to focus on? These basic questions will help guide your selection.
- Check the provider’s experience and expertise. Checking the pen testing provider’s track record and ensuring that the team has good experience carrying out pen testing for other customers is a good way to vet them.
- Find out what testing methodology would be used. Since there are different pen testing methodologies and techniques, it helps to understand what the pen testing provider would suggest. For instance, IS Partners has several pen testing services like external pen testing, internal pen testing, mobile application pen testing, web application pen testing, etc.
- Check the pen testing provider’s pricing plans. Depending on your budget, cost can be an important consideration. IS Partners provides pen testing services at very competitive prices without compromising on the quality of their services through the CheckBox pen testing service.
- Check if the provider offers post-testing support. Some pen testing providers offer support after the testing is completed to help with remedial actions to address vulnerabilities. Depending on your in-house capabilities, this can be a useful consideration.
Execute Penetration Testing With Ease and Accuracy—Contact IS Partners!
Choosing the right penetration testing technique is essential for effectively assessing your organization’s security. White box testing offers an in-depth examination of your system’s internal workings, while black box testing focuses on identifying vulnerabilities that external attackers might exploit.
Understanding these differences helps you select the appropriate method based on your specific needs and environment.
What Should You Do Next?
Take the next critical steps to improve your cybersecurity posture today!
Evaluate your organization’s security requirements to determine which penetration testing technique aligns best with your goals.
Consider the potential impact on your live environment, particularly for critical systems, before implementing tests.
Consult with IS Partners for expert guidance on selecting and executing the right penetration testing strategy tailored to your needs.
Ready to enhance your security posture? Contact us today to learn how we can support your penetration testing efforts!











