Business practices from a decade ago may seem nearly unrecognizable to today’s professionals—even those business leaders who were around a decade ago. That’s pretty much how everything is in 2020. The boundaries that once slowed progress and change evaporate more rapidly with each year.
As you work to keep up with all the restrictions and advancements that apply to your service organization and clients, it’s easy to get caught up in the fray and inadvertently set compliance matters on the back burner. Of course, you know how risky this type of delay can be, no matter how brief.
With an increasing threat of data breaches and even cloud-based security threats, it is important that you move SOC 2 security compliance efforts back to the front burner. It may seem difficult to imagine juggling one more project. But this one is essential, and it offers peace of mind for you and your clients. That alone makes it worth the commitment and effort.
See our foundational overview of What Are SOC 2 Audits and How to Stay Compliant.
4 Areas of Practice Critical to SOC 2 Security
Compliance with the SOC 2 reporting platform can make a huge difference for your organization, stakeholders, and clients. It provides tested tools to help fortify your business against determined hackers and cyber criminals while maintaining productivity.
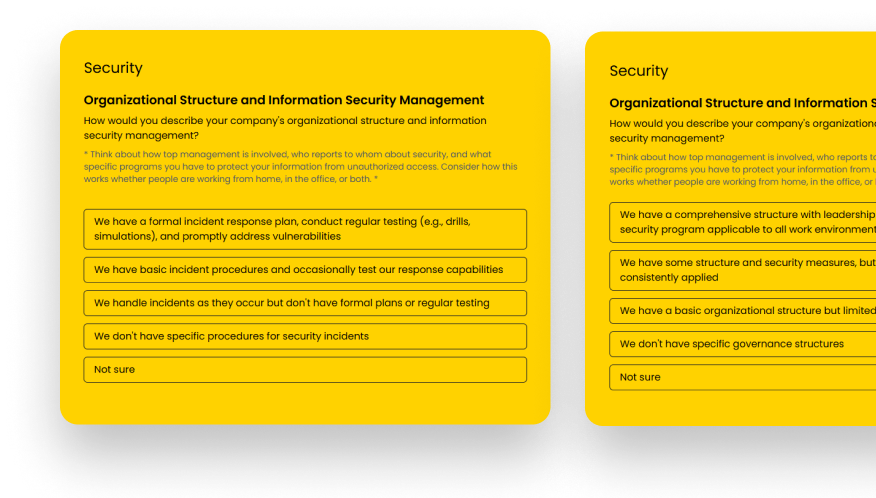
Our team came up with four areas of security practice that are crucial for SOC 2 compliance. We believe these serve as an excellent guide to best practices and daily operations. Plus, they will assist your efforts focused on achieving and maintaining SOC 2 compliance.
1. Conducting a Scoping and Readiness Assessment.
Conducting a scoping and readiness assessment is a logical place to start. This important exercise helps to ensure the long-term success of an audit through reviewing the health of the operating environment.
A comprehensive scoping and readiness assessment can help unearth any deficiencies in your internal control environment, such as any inefficient processes and procedures, before launching your annual SOC 2 audit. This gives your team the opportunity to remediate them before spending thousands of dollars on the official SOC 2 audit report process. Identifying problems late in the process only adds to your auditing costs.
2. Monitoring for Known and Unknown Malicious Activity.
With processes and practices in place for optimized oversight of your service organization and its internal controls, you have the power to continuously monitor for any known malicious activity that may be lurking in the shadows. Monitoring covers all user access levels for unusual system activity and authorized, or unauthorized, system configuration changes.
Given the fast-paced nature of the internet and working in the cloud, you must also prepare for unknown malicious activity. The best strategy for combating unknown problems is to set a baseline for what normal internal environment activity looks like within your cloud environment. This makes it far easier to detect and identify abnormal activity.
3. Developing and Implementing Functional Anomaly Alerts.
Given the current threat landscape, you will likely—at some point—experience a security incident. It is probably less common for organizations to go completely untouched and unscathed by cyberthreats today.
In order to respond quickly to a threatening event on the horizon, or in action, your team must have and be able to demonstrate sufficient alerting practices and procedures. In case of any unauthorized access—or access attempts—are made to customer data, you can jump into action and deliver the necessary response. This includes taking proper corrective action in time to avoid danger or incur the least possible damage.
To avoid false positives that leave you and your team scrambling for nothing, develop a process that alerts you only when activity deviates for standard operating procedures, as defined for your service organization’s unique operating environment.
SOC 2 helps in this regard by requiring businesses to set up alerts for any activities that result in the following unauthorized behaviors:
- File transfer activities,
- Modification or exposure of controls, data or configurations,
- Unusual login access, privileged file system or account alteration attempts.
Essentially, anything outside of the parameters set for your specific internal control environment can be programmed to trigger an anomaly alert.
4. Keeping Detailed Audit Records for Actionable Forensics.
Detailed audit records give you a historical reference to the causes and corrective actions related to attacks that your service organization has experienced. They can provide a reference point for developing responses to current and future threats. These records provide deep, contextual insights to assist eventual remediation efforts.
Following are two key insights that an audit trail can provide:
- The breadth and impact of a specific attack and the source point.
- Any addition, modification or removal of key system components.
With the detailed audit trail information readily at hand, you can perform actionable forensics exercises, such as determining:
- Where and how the attack originated.
- Where and how the attack proceeded once it made its way into the system.
- What parts of the system were ultimately impacted.
- The nature and severity of the impact.
- What the next move should be for response and remediation.
Does Your Service Organization Need Help Defining Security Practices?
If you are looking for ways to achieve efficient, on-time, and on-budget SOC 2 compliance, talk with IS Partners, LLC. We are the industry leaders in SOC 2 services and we are ready to help your service organization.