Overview
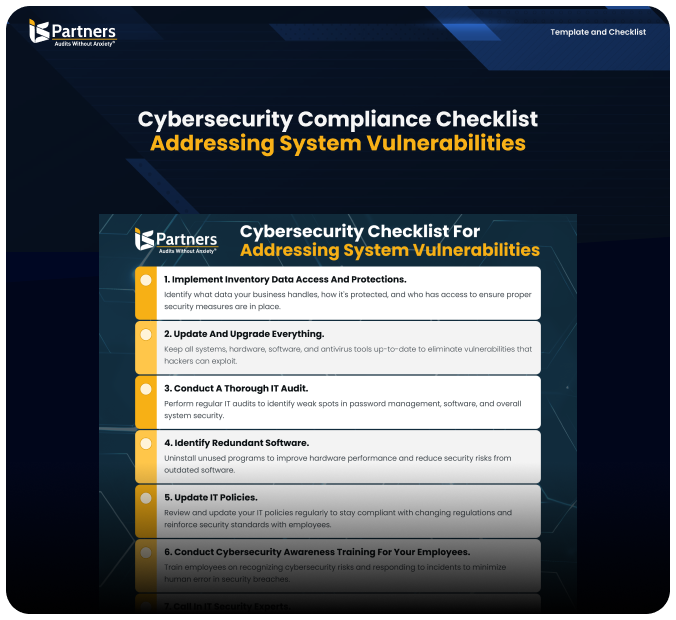
This Cybersecurity Compliance Checklist is your essential guide to identifying, mitigating, and managing system vulnerabilities. Designed to provide a step-by-step framework, it empowers organizations to strengthen their cybersecurity practices, meet regulatory requirements, and protect sensitive data.
How to Use
1
Follow the 10-step checklist to prepare effectively for your cybersecurity compliance audit.
2
Use this guide to identify sensitive data, implement required controls, and ensure all necessary documentation is in place.
3
Regularly consult the checklist to evaluate and improve your organization’s cybersecurity posture and compliance readiness.
4
Share with your team to ensure that all stakeholders are aware of their roles in maintaining cybersecurity compliance.
Questions? Speak with a specialist
Questions about compliance? Book a free call with our experts!
Staying ahead of compliance regulations is not just a necessity—it’s a strategic advantage. Our compliance specialists understand the complexities of IT compliance and the importance of aligning it with your business goals.
What you’ll get…