SOC 1 vs. SOC 2: What Type of Audit Does My Organization Need?
If your company provides services to other companies, those services may have an impact on your customers’ financial reporting. As a result, your customers’ auditors may need assurance that the controls surrounding your services are designed effectively, and in some cases, operating effectively. What does SOC 1® and SOC 2® stand for? They are a way to provide that assurance is by undergoing a Service Organization Control (SOC) audit.
We can define SOC reports as a document that helps service organizations “that operate information systems and provide information system services to other entities, build trust and confidence in their service delivery processes and controls through a report by an independent Certified Public Accountant,” according to American Institute of CPAs (AICPA). Then, when we look closer at SOC 1 vs. SOC 2 audit reports, it’s easy to see the distinct differences. SOC reports serve to assist your customers who need to comply with audit requests from outside accounting firms, so the results of your SOC audit help make those audit processes smoother.
As a service organization, you bear certain responsibilities regarding different facets of your business to each of your clients, according to the AICPA. SOC reports are designed to help meet your needs in fulfilling specific client (or user entity) requests, which come in the form of SOC 1, SOC 2 or SOC 3.
Key Takeaways
2. SOC 1 tests controls that meet the identified control objectives, whereas SOC 2 identifies and tests controls that meet the criteria.
SOC 1 vs. SOC 2: How Are They Different?
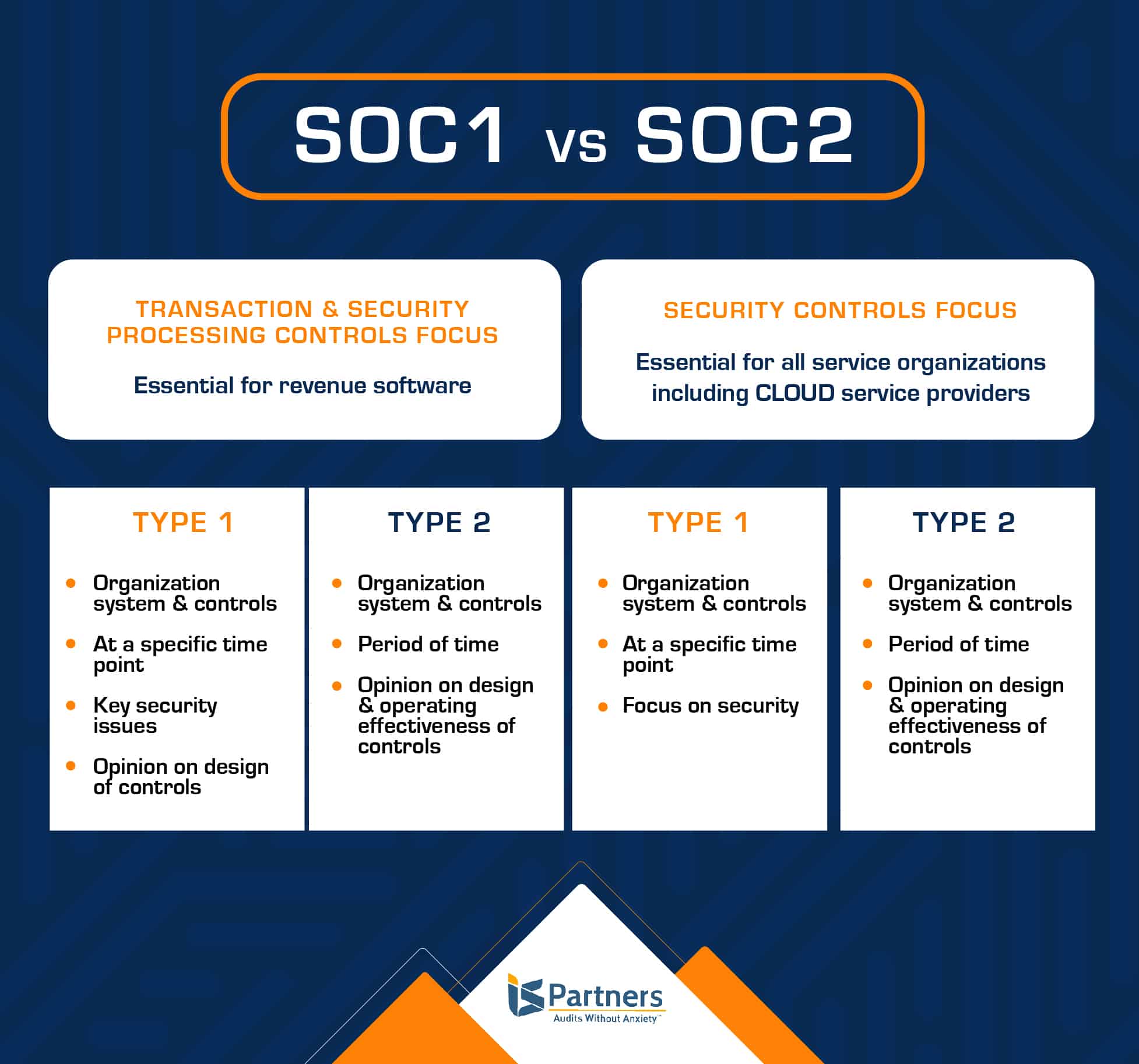
The main difference between SOC 1 and SOC 2 is that SOC 1 reports focus on financial data control, while SOC 2 reports have a more extensive scope that covers availability, security, processing integrity, confidentiality, and privacy. SOC 1 and SOC 2 are both types of Service Organization Control reports that provide assurance on an organization’s controls, but they differ in their focuses.
SOC 1 for Service Organizations: ICFR
The SOC 1 audit addresses Internal Control over Financial Reporting (ICFR). Anything likely to be relevant to an audit of a user entity’s financial statements is the focus for a SOC 1 audit.
Further, there are two different types of SOC 1 reports available:
- The Type 1 report offers the opinion of your auditor that your system is designed suitably to achieve the related objectives on a specified date.
- The Type 2 report contains all the same information as Type 1 but focuses on testing the controls to prove their effectiveness over a period of time.
Get our tips for preparing for your next SOC 1 audit here.
What is a SOC 1 Report?
Previously known as the SSAE 18, the SOC 1 report has a financial focus; it covers the service organization’s controls that are relevant to an audit of a user entity’s (customer’s) financial statements. Control objectives are related to both business processes and information technology.
A SOC 1 – Type I audit report focuses on a description of a service organization’s control and the suitability of how those controls are designed to achieve the control objectives as of a specified date.
A SOC 1 –Type II audit report contains the same opinions as a Type I, but it adds an opinion on the operating effectiveness to achieve related control objectives throughout a specified period. SOC 1 audit reports are restricted to the operations management of the services organization, user entities, and user auditors.
Does My Organization Need a SOC 1 Report?
You probably know whether your organization needs to perform SOC 1 reports for your customers, but it might help you to ask yourself a few key questions to make sure you need to perform this particular report:
- Will a SOC 1 report serve as a reliable tool for your customers and their auditors when performing an audit? This function is the cornerstone of a SOC 1 Type 1 report and is invaluable to helping your customer undergo a smooth audit that leaves little room for questions from outside auditors.
- Will the SOC 1 report prove useful to your customers who need to comply with the Sarbanes-Oxley Act (SOX) of 2002? A SOC 1 report serves as a solid tool that will help your customers comply with financial laws and regulations, improve adherence to corporate responsibilities, and combat corporate and accounting fraud.
- Will the SOC 1 report help form strong relationships with stakeholders and customers? One benefit of a SOC 1 report is that it helps boost trust and confidence in your service organization among stakeholders. A SOC 1 provides an easily accessible report of your processes to create transparency and assurance.
The AICPA clarifies that this type of SOC report is for service organizations that directly impact, or has the potential to impact, their clients’ financial reporting. It is also relevant to user entities’ internal control over financial reporting.
SOC 2 for Service Organizations: Trust Services Criteria
The SOC 2 audit is used when a company outsources technological and data-related services, such as data hosting, colocation, data processing and Software-as-a-Service (SaaS).
The SOC 2 report focuses on the controls at a service organization that relate to the security, availability, processing integrity, confidentiality, and privacy of a service organization’s technological systems, operations, and regulatory compliance.
This report is particularly helpful in areas that include organizational oversight, vendor management programs and regulatory oversight.
What is a SOC 2 Report?
The SOC 2 report was previously known as the SSAE 18 standard, it’s also referred to as a SOC 2 attestation report. It was created in part because of the rise of cloud computing and business outsourcing of functions to service organizations.
These are called user entities in the SOC attestation reports. Liability concerns have caused a demand in assurance of confidentiality and privacy of information processed by the system.
The meaning of SOC 2 is a report that attests to the availability, security, processing integrity, confidentiality and privacy of a service organization’s controls.
The report addresses controls related to operations and compliance, as outlined by the AICPA’s Trust Services criteria in relation to its services, operations, and compliance. A service organization may choose a SOC 2 report that focuses on anyone or all five Trust Service principles and may choose either a SOC 2 Type I certification or a Type II certification.
A SOC 2 attestation report includes a detailed description of the service auditor’s test of controls and results. The use of this report is generally restricted.
See the steps on how to prepare for a SOC 2 Audit.
Does My Organization Need SOC 2 Attestation Report?
SOC 2 attestation requirements govern engaged, technology-based service organizations which store client information in the cloud. This includes SaaS providers and other cloud service platforms.
Who Receives & Reviews SOC Reports?
The user entity’s auditors are responsible for an organization’s internal controls, regulatory and IT compliance and should obtain and review the SOC 1 or 2 report.
Anyone in vendor compliance, internal audit, operations manager, IT management and legal departments may be interested in understanding the control structure of the service organization. Key components to consider when undergoing a SOC report:
- Does the report include testing the operating effectiveness of controls for a specific period of time, or does it only cover a specific point in time?
- For SOC 1 reports, does the time period of the tests of controls provide appropriate coverage for the specific fiscal year?
- Does the system or report scope comprehensively outline the services that you outsource?
- Does the scope of the system include a sub-service organization? Has the service organization utilized the carve-out or inclusive method?
- Review any testing exceptions to determine impact of your assessment of the service organization.
- The service auditor’s professional reputation.
Reading & Understanding Compliance Reports: SOC 1 vs SOC 2
Here are the foundational steps in gleaning the right type of information from SOC 1 and SOC 2 compliance reports.
Identify Who Issued the SOC Report.
This AICPA requires that all SOC reports be issued by an independent CPA firm. With each submitted report, check that their CPA license is up to date and that the firm has the appropriate information technology or information security certifications. This provides assurance that the firm undergoes peer review every three years to ensure that the firm is up to speed on its accounting and auditing practices at the time of your audit.
Identify the Scope of the SOC Report.
SOC 1 and SOC 2, in particular, provide clear scopes from which you may choose. With SOC 1, you will be looking at financial statements to determine the internal controls at an organization. Here, you can decide whether you need to read and interpret the details from a specific date, or dates, or you may choose to look at a specific period. With SOC 2 reports, you’ll need to identify which of the Trust Services Criteria are covered in the audit.
Additional scope parameters that may be included:
- Specific locations
- Certain date or timeframe
- Systems involved
- Responsible staff members
- Business applications and technology platforms involved
- Processes that focus on internal control over financial reporting
While many of these parameters are applicable to each type of SOC report, double-check that all the language corresponds to your specific report. Determining the scope will help make it easier to read and understand the report.
Review the Auditor’s Opinion of the SOC Report.
The SOC examination report contains an independent auditor’s opinion regarding the description of the service organization’s system and whether it is presented fairly. The auditor also provides an opinion on whether the controls in the service organization are suitably designed to ensure the security of the user entity. The auditor’s opinion is presented in four possible variations:
- Unqualified Opinion – This type of report is issued when the independent service auditor completely supports the findings, with no modifications.
- Qualified Opinion – Here, the auditor cannot deliver an unqualified opinion, but the qualified findings are not so severe that they warrant the issuance of an adverse opinion.
- Adverse Opinion – An adverse opinion is rendered when the auditor has come to the conclusion that the user entity should not rely on the vendor’s systems.
- Disclaimer Opinion – The auditor offers a disclaimer when they cannot express an official opinion because they could not obtain the necessary evidence required to establish their opinion.
To clarify, the best outcome for your business, as well as your relationship with your service organization, is to receive an unqualified opinion from their independent auditor. Any of the other opinion type should encourage you to dig deeper and evaluation the impact of any registered qualifications.
Make Note of Things That Need to Be Improved.
The practitioner will highlight areas that require modifications and controls that could be improved in the CUECs, deviations and responses, and points of non-compliance.
CUECs
The complementary user entity considerations (CUECs) are controls that your organization must implement. The SOC report will help you determine if those controls are applicable and whether you need to adopt and implement them to satisfy the CUECs.
Deviations and Responses
While you are seeking good results in a SOC report, you must also look at any shortcomings and deviations, as well as the possible impact of those deviations. If deviations threaten to negatively affect your business, you should work to mitigate or compensate for them.
Exceptions or Points of Non-Compliance
As you review each control objective of a SOC report or the designated Trust Services Criteria, pinpoint any references to exceptions that took place during testing. This portion of the report is crucial since it helps illuminate any non-compliance issues and how they may impact your data and systems.
How Long Does it Take to Get SOC 1 vs SOC 2 Reports?
The time requirements for SOC 1 and SOC 2 are different SOC 1 reports may take a bit less time to complete depending on the availability of the relevant controls, SOC 2 is more stringent in that it examines policies and processes over a time period, with systems being assessed for at least six months.
A SOC 1 examination normally takes one to three months for Type I reports and six to twelve months for Type II reports if a company has controls in place. The audit may take longer if there are no controls in place.
For most businesses, a SOC 2 Report will take anything from six months to a year to complete. SOC 2 Type 1 Reports, in example, can take up to six months, but SOC 2 Type 2 Reports usually take at least six months and often last a year or longer.
“The process for achieving SOC 1 compliance is longer from a readiness standpoint. I’d say that it takes considerably longer to start from scratch and get certified for SOC 1–as opposed to approaching a SOC 2 audit for the first time–but the audit is done the first time, the organization should be all set. There isn’t much difference in time and effort; recertification will likely require virtually the same amount of effort as a SOC 2.”
– Robert Godard, partner at I.S. Partners is specialized in audits of IT controls and infrastructure, financial statements, SOC 1 and SOC 2 audits, HITRUST assessments and more.
Many factors influence these times, resulting in considerable variations from one company to the next. Companies with more complex and diversified IT and cybersecurity infrastructures, for example, would likely need more time to complete the audit procedure required for a SOC 2 Report. The number, kind, and location of users associated with the organization (i.e., on-premise or remote workers) will also influence the auditor’s evaluation scope.
Related article: Prepare a Great Written Assertion for Your SOC 1 Examination.
How Do You Evaluate a SOC Report?
If you are evaluating a SOC report performed on one of your organization’s vendors, or potential vendors, pay attention to the controls that have the most impact your business’s security as you review the report. Any controls that have an adverse or disclaimer opinion sited are clear points for concern. You must decide which of your vendor’s controls are critical and evaluate if there are any exceptions or compliance issues that could increase risk levels by working together.
What Should You Look for When Reviewing a SOC Report?
For a SOC audit performed on your organization, specifically, you should review the auditor’s opinion, CUECs, points of non-compliance, as well as deviations and responses.
SOC 1 vs. SOC 2 Can Be a Difficult Decision – We Can Help
I.S. Partners, LLC is the leading provider of internal audit services for businesses around the world. We perform SOC audits both in person and remotely. Let one of our trusted experts help meet your business goals. Request a quote to get started.
FAQs
Glossary of Terms
SOC Reports: These are documents that help service organizations assure their customers of their service delivery processes and controls. These reports are composed by an independent Certified Public Accountant (CPA).
Service Organization: An entity that operates information systems and provides system services to other businesses. They have the responsibility for the services they offer and for the secure protection of sensitive data.
AICPA: The (American Institute of CPAs) is a governing body that defines standards and procedures for creating SOC reports.
SOC Audit: A systematic review and examination conducted by an independent body, to validate the accuracy and authenticity of the organization’s data and records.
Client/User Entity Requests: Requirements or conditions stipulated by an organization’s clients or user entities that need fulfillment.
Controls: Procedures and policies in place within a service organization that help manage certain risks and ensure reliability in financial reporting.
SOC Auditor: An independent professional (generally a Certified Public Accountant) who performs an audit to assess the validity and reliability of a company’s records or operations.
SOC 1®, SOC 2® and SOC 3® are registered trademarks of the AICPA (American Institute of Certified Public Accountants). The AICPA® Trust Services Criteria for Security, Availability, Processing Integrity, Confidentiality, and Privacy is copyrighted by the Association of International Certified Professional Accountants. All rights reserved.